Managing Third-Party Cyber Risk
Discover the five areas you need to focus on when assessing third-party risk, or the uplift of your current efforts.
Getting Started
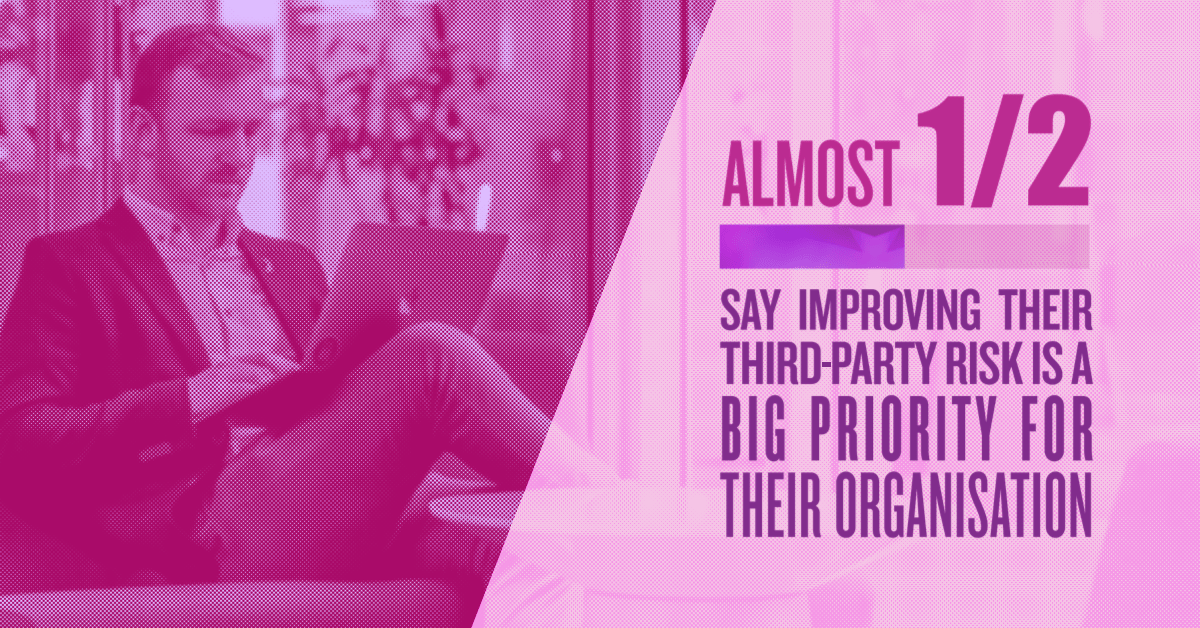
Managing third-party cyber risk can be a complex and daunting exercise, especially for large organisations with a vast array of suppliers and vendors. However, it’s an increasingly important area to focus on, as threat actors look to leverage third-parties as a “back door” to enter your environment.
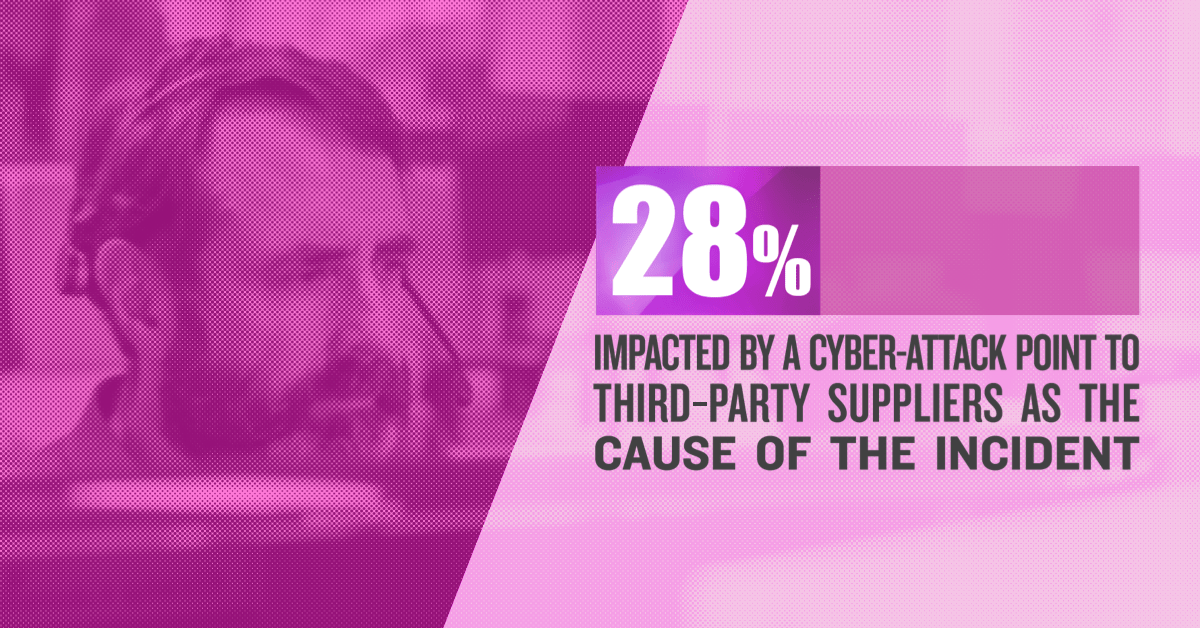
A recent survey by Kordia found that 28% of business impacted by a cyber incident or attack in the past 12 months involved a third-party.*
If you’re looking to embark on a programme to assess your third-party risk, or uplift your current efforts, here’s five suggested areas to focus on first.
1. Understand your third-party networks
The first step is to understand what third-parties you use, across all aspects of your organisation. Undertaking an audit and developing a register that lists out every third-party vendor, what they offer and what data they have access to will give you a clear view of what risks you are facing. A good question to ask of each supplier is whether they provide support or hosting of services, or whether they have access (physical or virtual) to your company or your customers' data? If the answer is yes, this means you should definitely be assessing them from a security perspective.
You’ll also want a view on what suppliers your suppliers use – your fourth and fifth parties. For example, you may outsource your IT services to a business, who may in turn use a project management tool that is fed data on your company. Ideally, your partners should give you a clear picture of how and when access to your data and systems may be given to other businesses they work with, so you can stay on top of any potential risk.
2. Prioritise based on risk
You may use hundreds, even thousands of suppliers and third-party platforms – but there will be several key offerings that are fundamental for your operations – perhaps a customer management tool, website, or billing software. These are the systems that, if compromised, could grind your business to a halt.
Once you determine what the key third-party platforms and software are for your organisation, you can start to focus your resources more sharply and map out a plan for protecting these. Tackling those more critical risks will dramatically reduce the likelihood of your business being seriously impacted should one of those third-parties be compromised.
3. Third-party cyber risk management is a team sport
Third-party cyber security needs a collaborative approach. The best approach combines expertise in procurement, IT and cyber security to understand processes around acquiring new third-party software and platforms, and how to insert cyber security considerations into this. This is especially the case when procurement is decentralised, and different departments take care of their own purchasing.
This approach will make it easier to implement best practice management of your third-party cyber security risk – such as implementing tools to help automate and manage third-party risk and factoring in third-parties into your defensive monitoring and vulnerability management programmes.
4. Determine who has access
Who has access to your data stored in third-party systems? Do third-parties have permissions or access rights into your own systems?
Makes sure you regularly review the user accounts for your core systems, so you can close off access when circumstances change – for example when someone leaves the company, or if you stop using a particular vendor.
Also think about physical access – keep track of who comes into your premises and what they are accessing or working on. It sounds absurd, but some of our “Red Team” engagements have seen Kordia's independent cyber consultants at Aura walk in through the front door, posing as IT workers, and gaining immediate access to the company’s IT infrastructure – sometimes aided by “helpful” employees!
5. Your cyber incident response plans
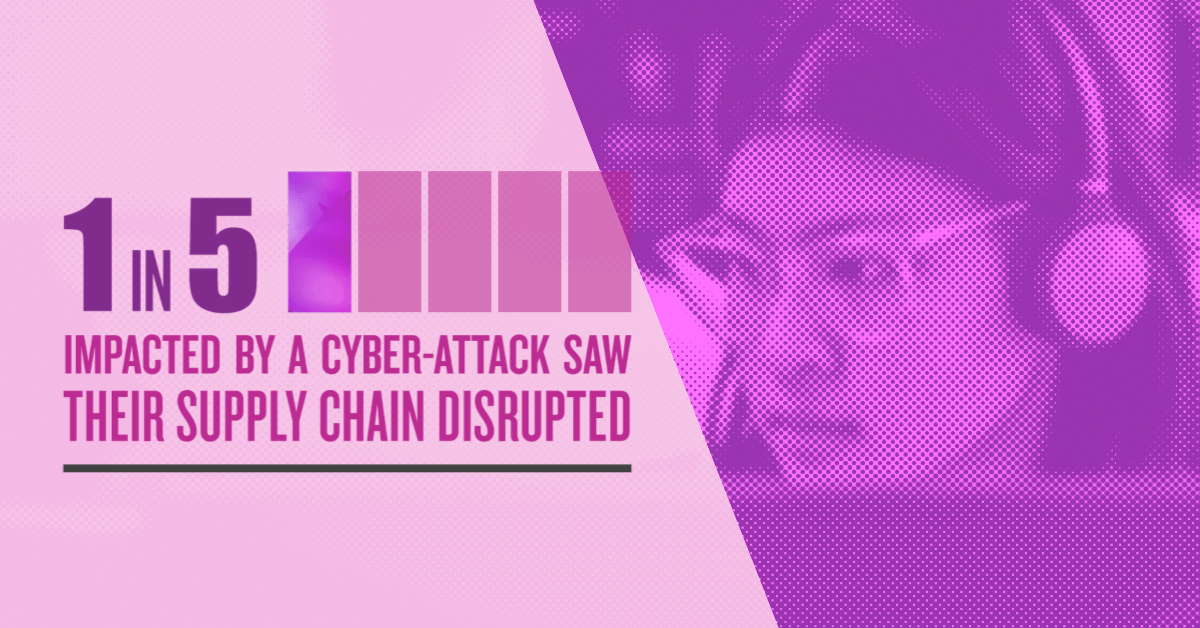
With a significant number of cyber-attacks coming through third-parties, it is a wise idea to plan around various scenarios that could befall your organisation’s partners and rehearse this as part of your incident response planning. You should have some sort of sense of how you’d react if a major platform was taken down due to a cyber-attack, or what data or systems would be at risk if a key piece of software was compromised, as well as your supplier's obligations in this instance.
You may even want to extend an invite to your key third-party partners to rehearse alongside you in an incident response simulation or tabletop event. This would ensure you’re aligned on how you’d both respond to a cyber incident – as well as making sure your third-parties have the right capabilities and preparation in place to support you during a breach, as well as your supplier’s obligations in this instance.
Like to learn more? Download our Executive Incident & Response Checklist |

Ready for more information?
Kordia’s independent cyber consultants – Aura Information Security work closely with businesses to help them manage their third-party cyber security risk, with actionable insights and advice on the right approaches and tools to tackle this in the most effective way.
If you need support getting on top of your third-party suppliers, speak to one of our consultants or your Kordia representative for more information.